
Malware: Type of malicious software that is designed to damage, or gain unauthorized access to a network.

Phishing: Common form of social engineering that involve tricking users into revealing sensitive information.

Distributed Denial of Service (DDoS) Attacks: Attacks involve overwhelming a server or network with traffic in order to render it unusable.

Zero-Day Exploits: Type of malicious software that is designed to damage, disrupt, or gain unauthorized access to a computer system or network.

Supply Chain Attacks: attacks involve compromising a vendor or supplier in order to gain access to an enterprise's systems or data.
Founded in 1984, Cisco is widely recognized as a leading provider of enterprise networking solutions, with over 80,000 employees in 95 countries around the world.
After four decades, Cisco's attention has shifted towards securing multiple endpoints and cloud computing. The company's objective is to simplify its security offerings by developing the Cisco Security Cloud, which plans to be the industry’s most open platform, “protecting the integrity of the entire IT ecosystem”. At present, the company's emphasis is on three primary areas:

In a post COVID world, requirements of cybersecurity have changed as businesses began to adopt a digital-first model. Cisco plans to help customers connect, secure and automate to accelerate their digital agility in a cloud-first world. Client priorities Cisco may help with:
Reimagine applications
Power hybrid work
Transform infrastructure
Secure enterprise
A possible approach Cisco has considered is to create a unified security platform that can seamlessly integrate multiple security products, offering users a more comprehensive and better streamlined security experience. By consolidating its security portfolio and simplifying its offerings, Cisco hopes to become a security product leader for organizations of all sizes to implement effective cybersecurity measures and safeguard their critical assets.
Moreover, Cisco recognizes that the current security landscape is highly dynamic and fast-paced, and it is crucial to keep pace with the evolving threat landscape.
The simple answer to the legacy problem is to replace the old system. However, three main factors hold enterprises from doing so-
“Legacy systems can’t be shutdown or updated easily... It takes years of effort to sunset them.”
- Excerpt from an interview with an information security lead
The challenges of adopting newer security tools are two fold-
“Affordable doesn't mean how much the system cost, but how much does it cost for my staff to learn it and run it.”
- Excerpt from an interview with a CTO of a startup
Convincing decision-makers to invest in preventative measures can be challenging as it may seem like an unnecessary expense. While the consequences of a security breach can be catastrophic for a company, such as loss of sensitive data or financial losses, it can be difficult to quantify the value of investing in security measures. Decision-makers may also be hesitant to invest in preventative measures as the return on investment is not immediately visible.
“Translating security risks into monetary value is a difficult task. The return of investment for securing an enterprise is hard to measure and convey.”
- Excerpt from an interview with a CISO of a University
Convincing decision-makers to invest in preventative measures can be challenging as it may seem like an unnecessary expense. While the consequences of a security breach can be catastrophic for a company, such as loss of sensitive data or financial losses, it can be difficult to quantify the value of investing in security measures.
The reframed approach puts a stronger emphasis towards Cisco’s goal of emerging as a competitor for the cybersecurity space by focusing on clients’ pain points and putting their needs at the forefront. The reframe also acknowledges the constantly changing landscape of cybersecurity and the fact that traditional security measures may not be enough to address emerging threats.
Incentivize employees with internal and external motivations to practice security hygiene.
Equip employees with the necessary resources to improve their security hygiene.
Incentivize employees with internal and external motivations to practice security hygiene.

Humans are often referred to as the “weakest link” in cybersecurity because they are susceptible to making mistakes and errors that can compromise the security of an organization's digital assets.
Ultimately, it is the actions and decisions of individual employees that can make or break an organization's cybersecurity posture. Understanding the behavioral archetypes of employees regarding cybersecurity awareness and cyber hygiene can help organizations tailor their training and awareness programs to better meet the needs of their workforce.
The Employee Behavior Quadrant is a theoretical model that aims to classify various employee behaviors and attitudes towards cybersecurity. This model comprises two axes:
Involvement axis describes the level of interest, participation, and commitment an employee shows towards cybersecurity practices. Involvement axis can further be divided into two categories:
Knowledge axis refers to the employee's awareness, understanding, and expertise in implementing cybersecurity measures.The knowledge axis can be classified into two categories:
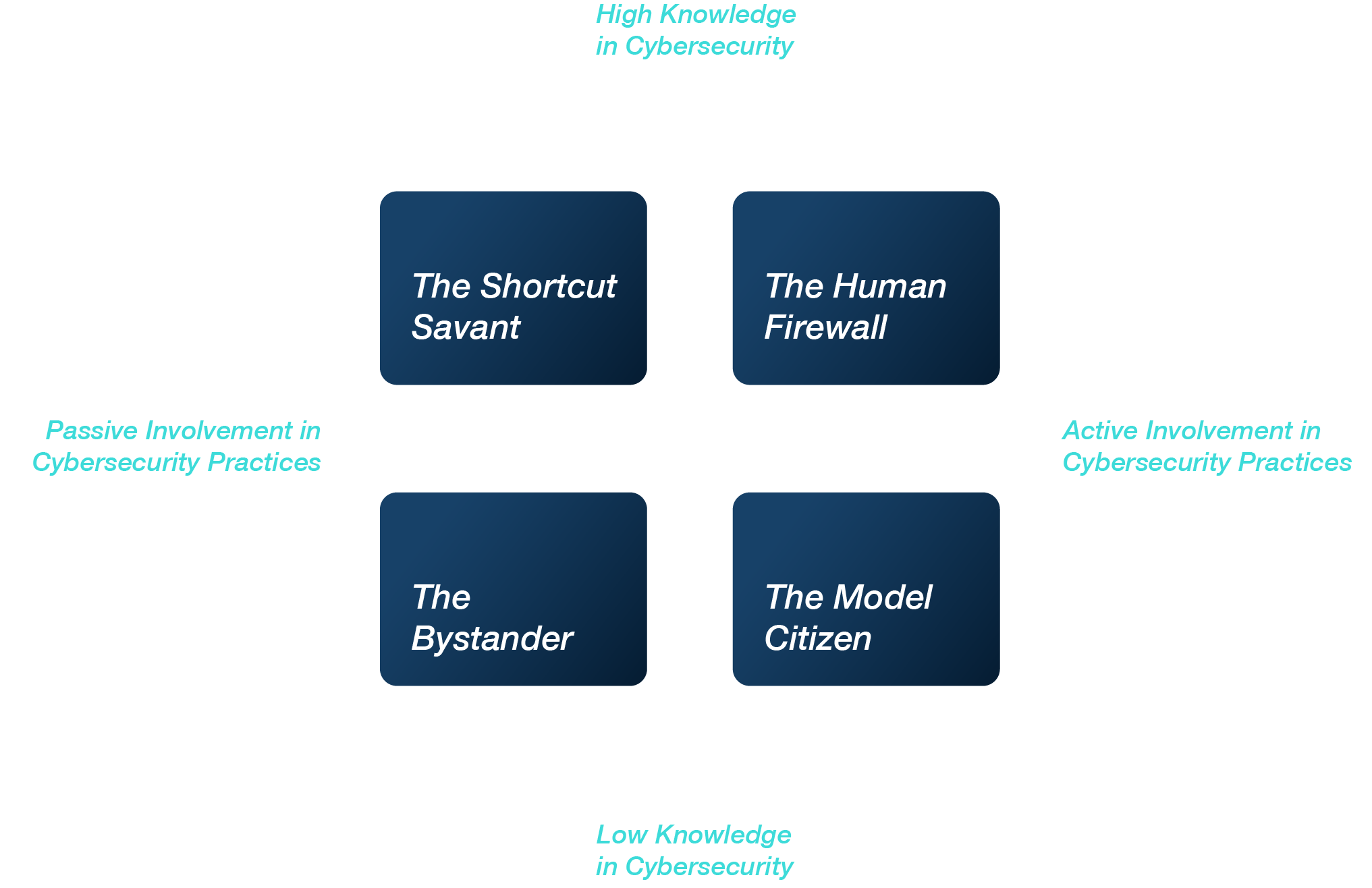
Employees in this quadrant are highly engaged and committed to following cybersecurity policies, and possess a good understanding of cybersecurity best practices. They are likely to be proactive in identifying and reporting potential security threats.
Employees in this quadrant have a good understanding of cybersecurity best practices, but are not actively engaged or committed to implementing them. They may need to be motivated or incentivized to become more involved in cybersecurity practices.
Employees in this quadrant are neither actively engaged nor possess a comprehensive understanding of cybersecurity best practices. They may require significant training and support to become more involved in cybersecurity practices. This quadrant represents the highest risk to an organization's cybersecurity posture.
Employees in this quadrant are highly engaged and committed to following cybersecurity policies, but without fully understanding the reasons behind these policies. They may require additional training and guidance to implement effective cybersecurity measures.
The emergence of social engineering attacks has prompted the creation of vendors that focus on developing software programs to help businesses and organizations defend against these types of attacks. These programs aim to simulate real-world phishing attacks and provide employees with a safe way to practice identifying and responding to these types of attacks.
Technical advancements like 2FA and zero-trust security models are becoming more prevalent in organizations' cybersecurity strategies. These tools can help protect against a range of attacks, from password cracking to insider threats. However, these approaches might give the wrong impression that humans can be entirely out of the picture of cybersecurity posture.
Organizations are increasingly using monitoring and metrics to track employee behaviors and violations of cybersecurity policies. This can include metrics like click-through rates on phishing emails or the number of security incidents reported by employees. However, while these metrics can be useful in identifying areas for improvement, they don’t necessarily provide insights into the context, goals and motivations behind employee’s behavior.
Most of the solutions available in the market take a condescending approach towards employees and portray them as risks. This approach is ineffective as we rarely address the underlying issues and causes of security breaches. Instead, businesses need to empathize with employees and design cybersecurity solutions around their needs, goals, and social settings.

Taken from the landing page of a popular security awareness training solution, we can sense the negative tone against employees and end users. While employees are indeed more susceptible to making mistakes and errors, it isn’t reasonable to assume all employees would keep security at the top of their minds, if they don’t work in a cybersecurity team.
What leads to breaches in protocol? Three common recorded responses- “to better accomplish tasks for my job,” “to get something I needed,” and “to help others get their work done”. These three responses accounted for 85% of the cases in which employees knowingly broke the rules,” research records. Why does security stand as a deterrent which hinders an employee from their usual day-to-day workflow, causing them to override the rules?
People are substantially more likely to knowingly break security protocols on days when they reported experiencing more stress, suggesting that being more stressed out reduced their tolerance for following rules that got in the way of doing their jobs. What considerations should design of security make for workplace stress that induces employee complacency?
The connection between job design and cybersecurity is significant. Adhering to cybersecurity regulations can increase employee workload, so compliance should be rewarded like other performance metrics. This raises the question of what employees gain from paying attention to security policies, as it is not currently considered part of their job.
18% of policy violations occur because employees want to assist their colleagues, such as in BEC scams. This can lead to breaking protocol and making transfers without proper verification due to time pressure. The current security design does not support employees helping each other without compromising enterprise security. Ideally, employees should not have to choose between helping colleagues and breaking security rules.
Encryption and authentication are only effective if they are consistently used, but employees often override them for various reasons. The design of security tools often fails to address this issue. How can design be utilized to bridge this gap and promote consistent usage of security tools? Are barriers to entry and the challenges of maintaining consistent use of security tools adequately considered in the tool creation process? What role can design play in addressing these challenges?

Subha Ramkumar

Jacob Chen

Ian Clark

Parvathy Anand

Daisy Dai